


Cybersecurity Resource Center
Explore our cybersecurity resource center to learn more about how we help public safety and enterprise organizations defend against cyber threats.
Cybersecurity Resources
White Papers and Brochures

Cybersecurity Services Overview
Our security services span your mission-critical ecosystem and IT network, endpoints and cloud.

Managed Services and Support
An overview of challenges facing public safety and how our Managed Support and Services can help.

Endpoint detection and response
A strong cyber strategy includes advanced endpoint detection and response to fight today’s threats.

Update your endpoint security
Security controls and technologies that address threats have matured and are more cost effective.

Ensuring continuity of operations
With NSOC, our advanced systems facilitate Emergency Services-grade monitoring and management.
Protecting PSAPs from cyber attacks
Despite being engineered for security, PSAPs are increasingly being targeted by threat actors.

Comprehensive Advisory Services
Prevent and respond to cyber threats quickly and meet compliance requirements.

Cybersecurity Services for ASTRO
Our cybersecurity solutions are designed to protect our industry-leading ASTRO radio systems.
Solution briefs and fact sheets

Cybersecurity Essential Services
Our cybersecurity essential services help you maintain the confidentiality, integrity and availability of your systems.

EDR for ASTRO
The benefits of Endpoint Detection and Response (EDR) for ASTRO Managed Detection and Response (MDR)

U.S government advisory services
We have built a portfolio of cybersecurity products and services to support the Federal government.

Discover system vulnerabilities
Penetration testing assesses the effectiveness of your technical controls, policies and procedures.

Reduce network vulnerability
Not all attacks can be stopped - but are you doing everything you can to protect your technology?

Ensure compliance and fight attacks
Our experts can assess current conformance and create a plan to get you on the path to compliance.

Be prepared with tabletop exercise
Test people, processes and technology with a tabletop exercise to prepare before disaster strikes.

Cloud security services for IT
Adopt cloud computing with the promise of increased efficiency, scalability and improved agility.

Advanced Threat Insights
Proactively searching for threats can help you prepare for potential issues and respond sooner.

Endpoint security for IT
Next generation (EDR) solutions offer more capabilities to detect and prevent cyber-attacks.

Protect PremierOne(R) CAD system
Monitor your PremierOne CAD system to detect and remediate potential cybersecurity threats.

Protect your FLEX™ system
Continuous monitoring finds and mitigates potential risks quickly, and contains advanced threats.

Protect your VESTA™ 9-1-1 system
Identify weakness through vulnerability scanning and enable faster response to cyber attacks.

IT network security services
Centralize security monitoring for on-premises IT networks.

Robust patching mitigates risk
Software needs to periodically be updated and patched to protect you from outside cyberattacks.

Cybersecurity training
Our Cybersecurity Hub provides timely, relevant and custom-fit cybersecurity training.

Office 365 security
ActiveEye gives you the visibility you need for Office 365 security.

Security patching upgrades
Cyber attacks are increasing and more impactful. Learn how security patching protects your network.

ASTRO Systems Authentication
An overview of ASTRO authentication features that protect critical communications.

Respond faster with ActiveEye
Our ActiveEye platform powers cybersecurity services, enabling the deployment of MDR capabilities.

Public Safety Threat Alliance
Learn more about the benefits of cyber threat sharing for public safety agencies.

Cyber Assurance Program
Our cyber assurance program provides services that help you integrate MDR into daily operations.

Protect LMR system availability
Protect ASTRO system availability with ASTRO System Monitoring

Federal ASTRO System Monitoring
ASTRO system monitoring for federal ASTRO systems

Commercial ASTRO System Monitoring
ASTRO system monitoring for commercial businesses

Protect ASTRO Systems
Maintain ASTRO system availability with Managed Detection and Response (MDR)
Videos and more
Protecting PSAPs Infographic
This infographic offers tips to protect Public Safety Answering Points (PSAPs) from cyber threats.
Learn moreCybersecurity services overview
Watch this short video to learn more about our managed and professional services.

PSTA Infographic
This infographic outlines risks to public safety and the value of shared threat intelligence.
View Infographic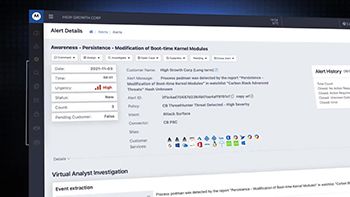
ActiveEye video
Learn about the ActiveEye Managed Security Platform and its features to safeguard your organization.
Watch the video
31 days of cybersecurity awareness
This infographic has 31 tips to help everyone learn more about cybersecurity.
See the Infographic
PSTA Webinars
View the quarterly webinars hosted by the Public Safety Threat Alliance (PSTA).
View Webinar
PSTA Full Membership Infographic
This infographic outlines all of the benefits of Full Membership in the PSTA.
View Infographic
PSTA Overview Infographic
This infographic details public safety cyber threat stats as well as a timeline of the PSTA.
Learn moreCybersecurity Services Overview
Cybersecurity is more important than ever before. Learn about the threats facing public safety
Cybersecurity for Public Safety
From ransomware to phishing Motorola Solutions is an industry leader in public safety cybersecurity
Cybersecurity Services Introduction
Maintain availability, integrity and confidentiality of public safety systems and data




